Shark jack что это
Payload Library for the Shark Jack by Hak5
This repository contains payloads and extensions for the Hak5 Shark Jack. Community developed payloads are listed and developers are encouraged to create pull requests to make changes to or submit new payloads.
About the Shark Jack
The Shark Jack is a portable network attack tool optimized for social engineering and opportunistic wired network auditing that makes network reconnaissance, exfiltration and automation quick and easy.
Generally, payloads may execute commands on your device. As such, it is possible for a payload to damage your device. Payloads from this repository are provided AS-IS without warranty. While Hak5 makes a best effort to review payloads, there are no guarantees as to their effectiveness. As with any script, you are advised to proceed with caution.
Payloads from this repository are provided for educational purposes only. Hak5 gear is intended for authorized auditing and security analysis purposes only where permitted subject to local and international laws where applicable. Users are solely responsible for compliance with all laws of their locality. Hak5 LLC and affiliates claim no responsibility for unauthorized or unlawful use.
Once you have developed your payload, you are encouraged to contribute to this repository by submitting a Pull Request. Reviewed and Approved pull requests will add your payload to this repository, where they may be publically available.
Please adhere to the following best practices and style guide when submitting a payload.
Payloads should begin with comments specifying at the very least the name of the payload and author. Additional information such as a brief description, the target, any dependencies / prerequisites and the LED status used is helpful.
Configurable options should be specified in variables at the top of the payload.txt file
About
The Official Hak5 Shark Jack Payload Repository
Shark Jack
Rapid and powerful network reconnaissance on a keyring.
Customisable payloads allow for fully automated network operations and data exfiltration.
Introduction
Functionality at a glance
Introduction
Functionality at a glance
Optimised for Penetration Testers and System Administrators, the Shark Jack is designed for discrete, rapid network reconnaissance, exfiltration and automation.
The Shark Jack draws from the field-proven Hak5 hardware framework: The Hak5 Payload Architecture, Multi-mode operation (Arm / Attack), LED feedback, simplified data exfiltration and a fully-featured SSH shell.
The default payload performs an nmap scan of the target network, saving data to the device for simple exfiltration.
Seriously Small
Always-Ready keyring form-factor
Single Switch Operation
One switch to attack, one to exfiltrate.
Fully Scriptable
Create or download payloads rapdily
USB-Charging
Supports Rapid USB-C Charging
What’s included
Technical Specifications
Shipping & Packaging
Compatible Systems
Plunder Bug Technical Resources
SHIPPING & PACKAGING
Do you provide free shipping?
For European Customers, orders over 100€ have free shipping.
For International Customers, orders over 250€ have free shipping.
Customers that qualify for free shipping can still select rapid shipping options.
When will I receive my order?
Average order times can be estimated below.
Average shipping estimates can be seen by selecting the destination country / region below.
Where do you ship from?
When will my order be dispatched?
What shipping options are available?
We provide four types of shipping:
How are import duties / customs handled?
Lab401 (ETOILE 401 SAS) is an EU-Registered entity. VAT is applicable to purchases delivered within the EU, with exceptions for VAT Registered entities. VAT is calculated at checkout. For your convenience, you can browse Lab401 with prices Including VAT and Excluding VAT.
Sales are contractual
Purchase Security Validation may be applied
To protect against credit card fraud, orders may be flagged for Purchase Security Validation. In this instance, we will reach out to the customer to perform a manual verification process.
Orders that are flagged for Purchase Security Validation are considered to be incomplete until validated. Our delivery deadline obligations begin only when an order is validated.
Delivery Protection
Is my delivery protected?
All Lab401 shipments are insured with the carrier.
We also provide an advanced insurance, Lab401 Delivery Protection.
Lab401 Delivery Protection means we remain fully responsible for the package right up to delivery. If the package is lost or damaged, the package can be resent immediately (48 business hours) upon receipt of proof.
For orders without Delivery Protection, lost or damaged packages will pass through the carrier’s protocols, which can take up to 30 days.
For orders that are time-sensitive, we recommend Lab401 Delivery Protection.
Delivery Protection can be purchased at checkout easily and cheaply.
Shark Jack: The Baby Yoda of Network Attack Tools
This past Black Friday, I went on a bit of a hacking tools shopping spree at Hak5. Today, I’m going to give a brief rundown of their Linux based network attack tool call Shark Jack (and why it’s similar to Baby Yoda). Shark Jack is to be used in environments where you are able to get physical access to wired network connections. The information below is for educational purposes only, and you should only use a tool like this on equipment/networks that you are authorized to do so.
Jump the Shark
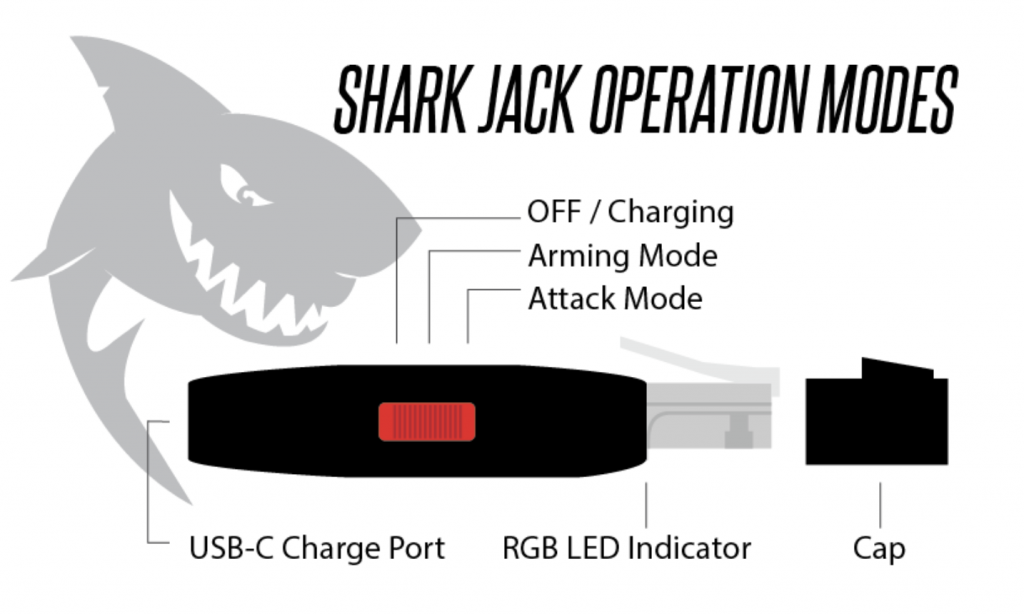
We’re going to get into some more in-depth information on things like payloads, firmware, folder structure and management in a little bit. Honestly though, as soon as I opened up the package, I just wanted to plug it in and see what it would do right off the bat (TLDR, you can plug it in, pull an IP via DHCP, and it runs a NMAP scan automatically). However, even that excitement needed to be tempered in order to understand how to turn it on and what the indicator light glowing from the RJ-45 plug meant.
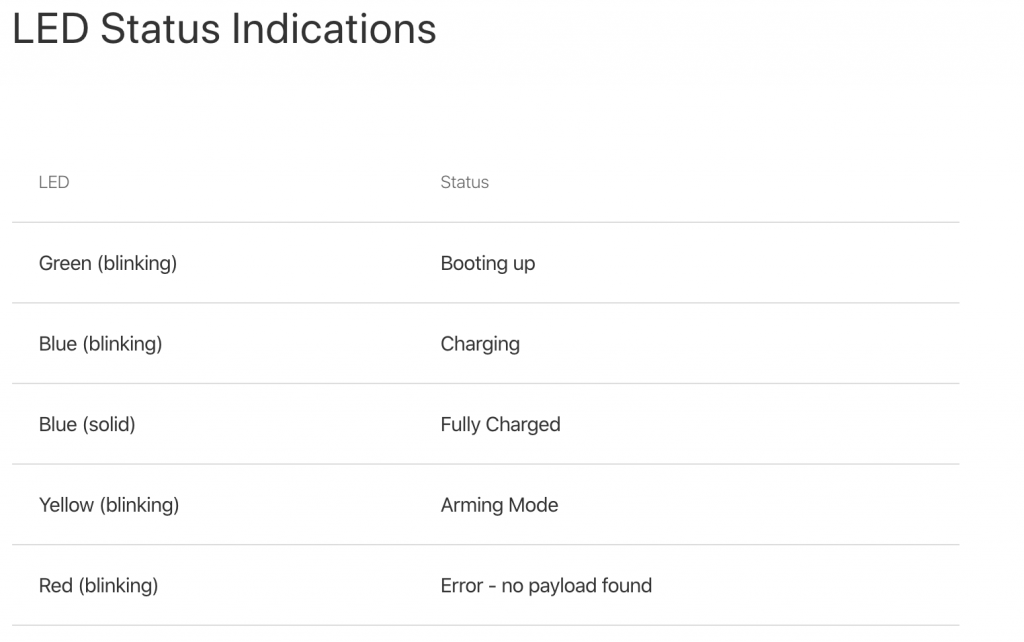
The diagram below taken from the Hak5 Shark Jack Basics page breaks things down pretty simply. First off, you need to make sure it is charged and this is done by plugging in a USB-C connection to the back of the device (it only takes a few minutes to fully charge). You’ll see it blinking blue when charging. Once fully charged, it will emit a solid blue light indicator.
Once it was fully charged, I was ready to go plug it into my test network and see what it would do. One thing to point out is to make sure not to overcharge the Shark Jack! Make sure not to leave it plugged in charging for an overly long extended period of time. Once it’s fully charged, it should provide 10-15 minutes of lifetime from the moment it’s turned on. So remember, this is for a short duration scan/recon. This, my friends, is why it’s like Baby Yoda. The Shark Jack comes in a small package, has the ability to use the force via bash/python payloads, it gets tired really quickly, and then has to go to sleep after doing its work!
At this point, it would also be a good time to review what the other LED status lights actually meant (I had already seen both version of the blue LED).
So, I pushed the red operation button to the far right (into “attack” mode) and plugged it into the LAN side of my test network. Once plugged in, it will start blinking green (meaning booting up) and then it will start blinking magenta (meaning it is scanning). Once the scan is completed, it will go to a brief solid green color.
After going through the brief process above, we need to reel back the excitement. We got way ahead of ourselves and now need to go back and read up on what the Shark Jack actually just did, how I can manage it, and what else we can do with. That being said, it’s a good feeling so far that you can take the device out of the package, plug it in, and it works (at least that is the impression so far… let’s see what loot it has for us inside).
The Real Deal
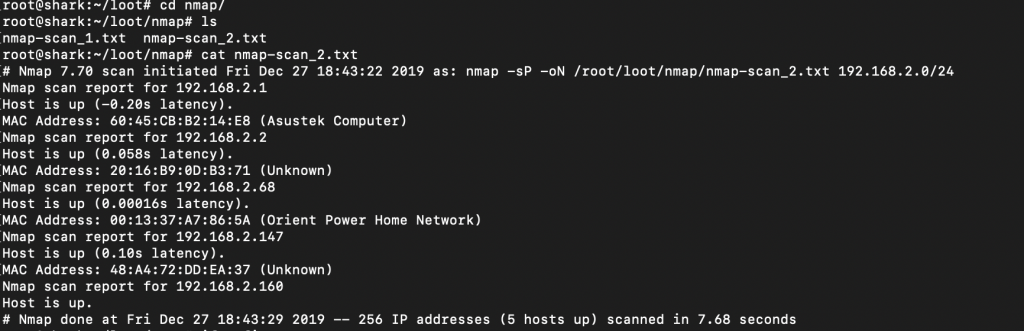
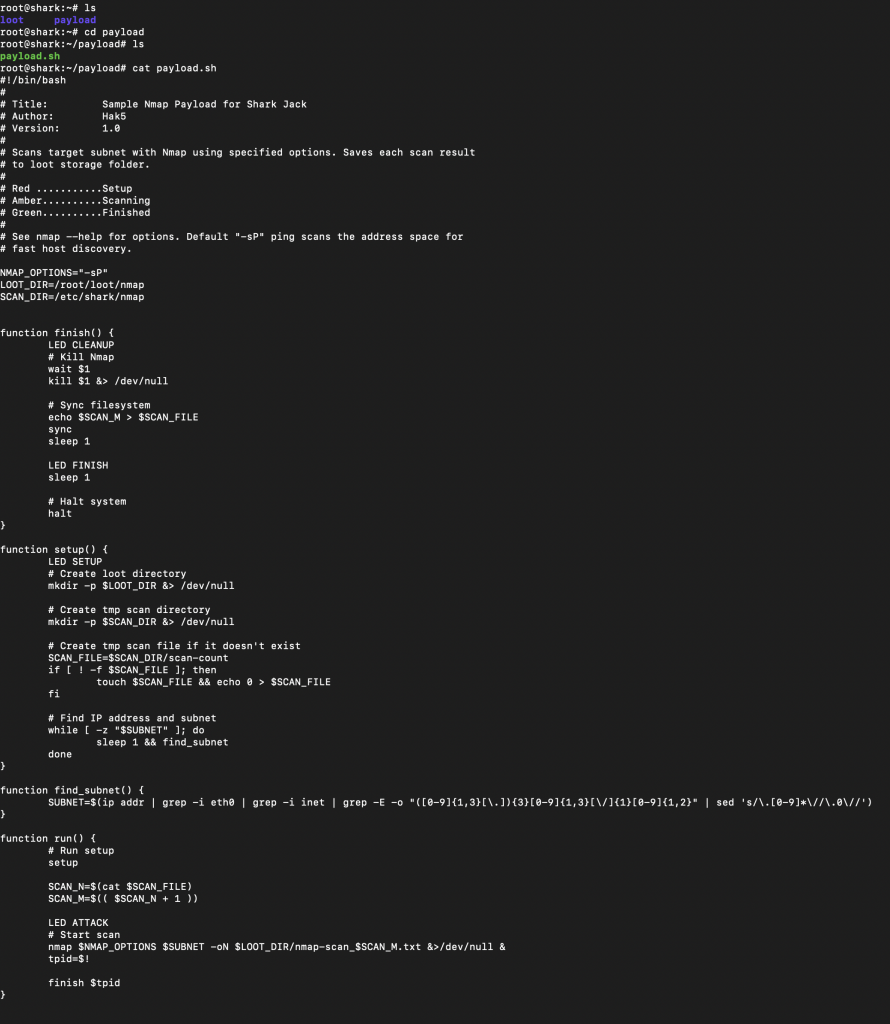
Now let’s get into some technical stuff about what happened behind the scenes. When set to the attack mode, the devices enables DHCP on the interface and pulls an IP address from the network. This is dependant on the connection you are plugging into being live/enabled, not running port security, and is offering up DHCP addresses. So, there is a hit or miss factor here. Depending on the environment, plugging the shark in could set off alarms. It then runs a payload, in this case a simple NMAP scan. This is a Linux based tool, so you can download other Linux tools onto it. You can also add your own payload instead. It will take bash or python payloads (more on this later).
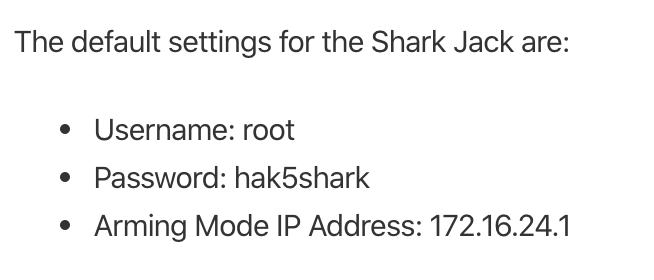
The primary way to access and manage the Shark Jack is by changing the mode selector to the “arming” mode. This means pushing the selector button to the middle position. Then you can take the device and plug it into and network connection on your laptop or PC to manage it. Of course, we would need the default credentials.
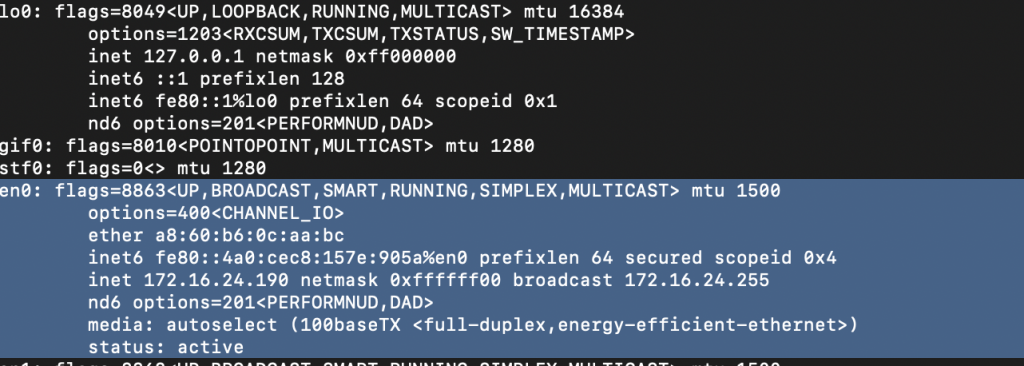
As you can see from the screenshot below, once I plugged it into my machine, it provided a network IP address in the 172.16.42.x range to my PC. I was then able to SSH in the box with the above credentials.
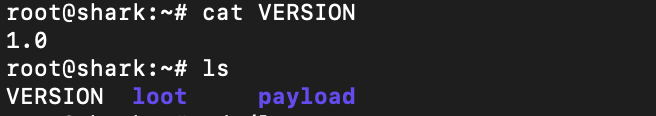
Exploring the Space
You get dropped in the /root directory and from there you really have three things to look at: the version, the loot directory, and the payload directory. Loot is wherever your payloads drop the data/logs from your scanning, and the payload directory is where said payloads are kept.
We can take a deeper dive into the payload to see what is going on. We could also modify this here if we wanted to have our NMAP be a bit more robust.
More Options
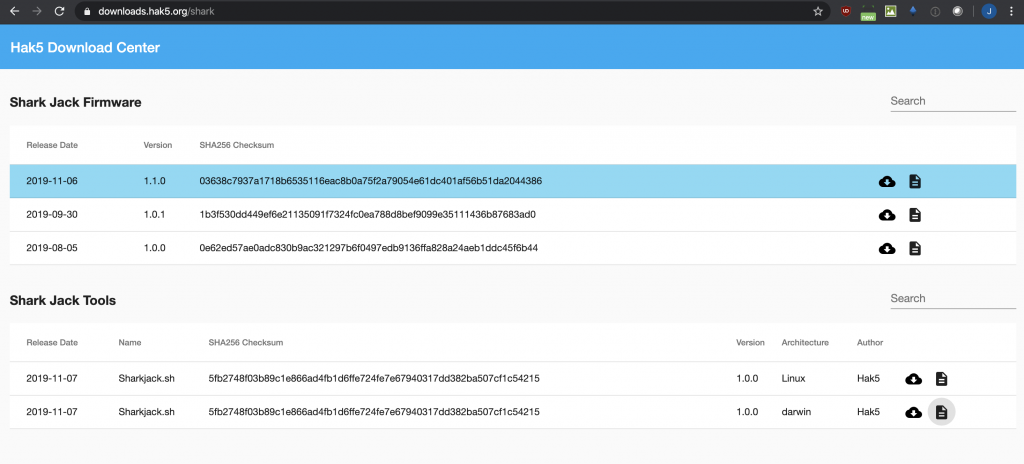
Now we have a basic understanding of the layout and what is going on, what else can we do with it? I wanted to see if there were any firmware updates that might provide some additional functionality. My device was shipped with 1.0.0 and the latest is 1.1.0. In going to update the firmware, I came across a nice Shark Jack utility that you can download that helps make managing the device a little bit easier (it will save you a few commands here and there). So first, I downloaded the Shark Jack Tools from the location below. I did have to “chmod +x sharkjack.sh” to make it executable (for those trying at home).
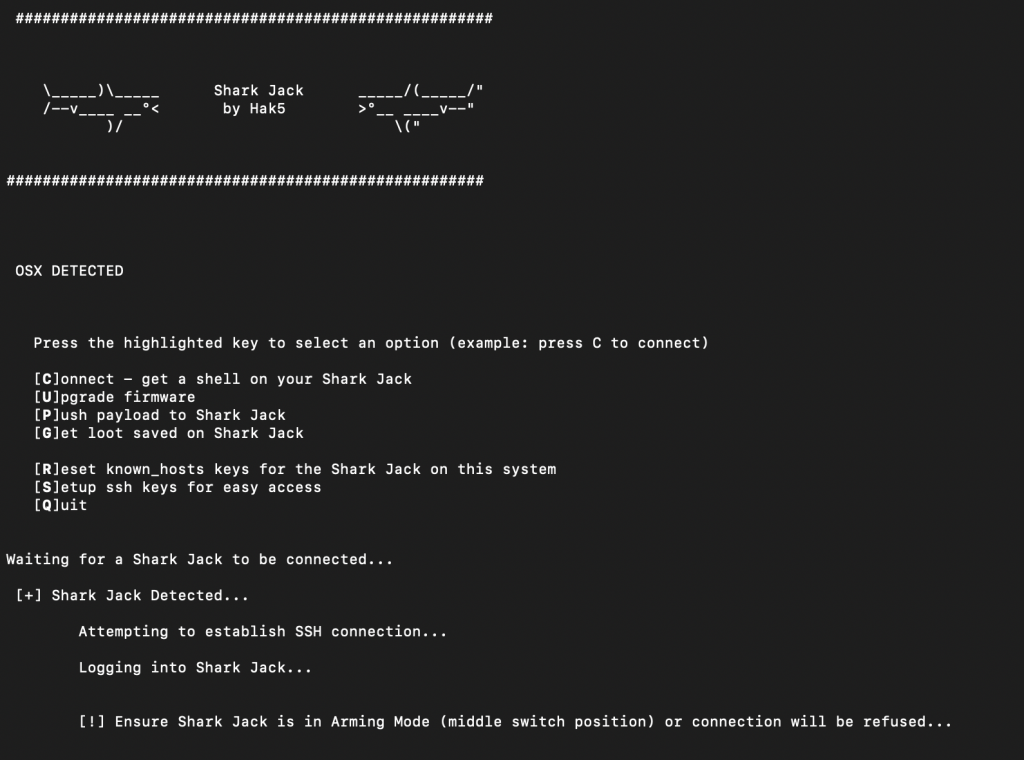
So, after running “./sharjack.sh” I got these neat little interface. This would streamline my firmware upgrade. I first chose “C” to connect, and after accepting the SSH key for the first time and using the default credentials, I was able to connect.
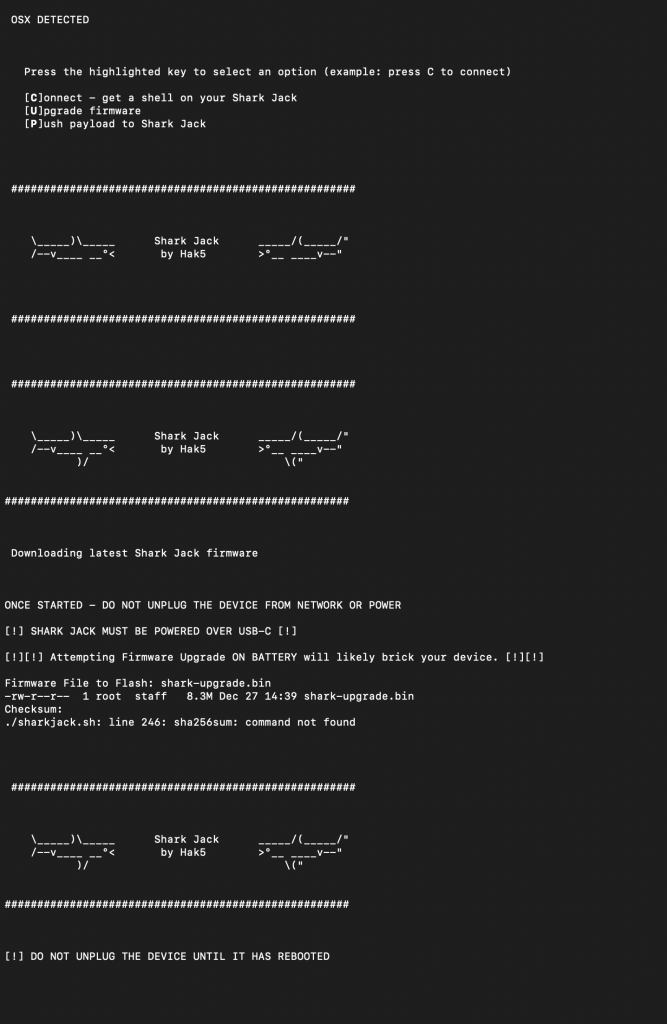
After verifying connectivity, I then decided to go the “U” route to upgrade the firmware. I made sure it had power connected to it and the total upgrade took a couple of minutes.
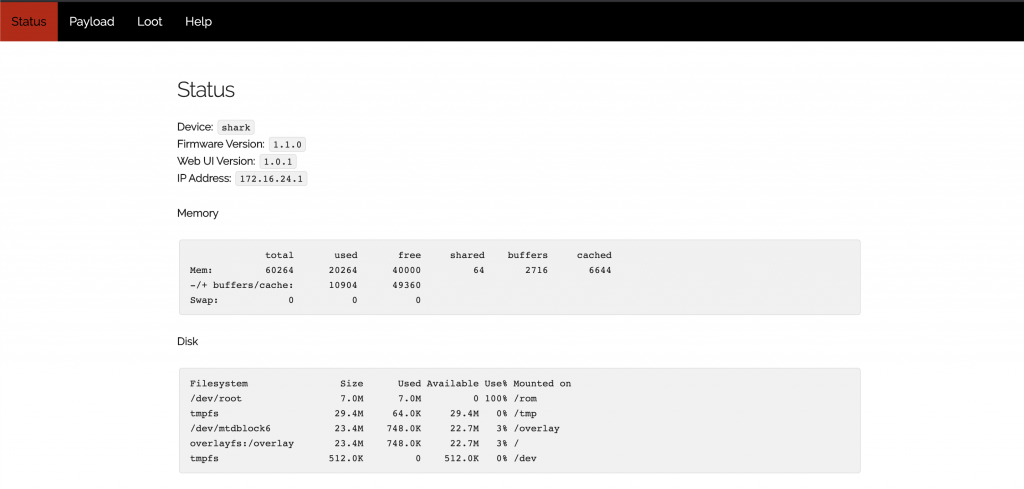
So, what do you get with the latest firmware upgrade? How about a snazzy new WebUI! You are now no longer burdened with the pain of the CLI and SSH connections 😛
On the serious side, this interface allows you to see both the current payload and any loot (scan logs) you might have collected. As well, it shows some health and configuration data about the device.
Raining Payloads
Besides creating or modifying your own payloads, Hak5 offers a few that they prominently feature on their website. The Sample NMAP Payload is the one that was tested above. The SSH IP Blinker is unique in that it turns on a SSH server, attempts to get an IP address via DHCP and then blinks the last octet of the host’s IP address. This could prove to be useful as one could then attempt to remotely access the device (with a good guess of the IP address) and upload additional payloads or tool sets to it. There are a lot of things that need to line up correctly for this to happen, but it is still cool in concept!
The above payloads can be found here with greater descriptions, as well as a few more additional payloads at the Shark Jack GitHub repo.
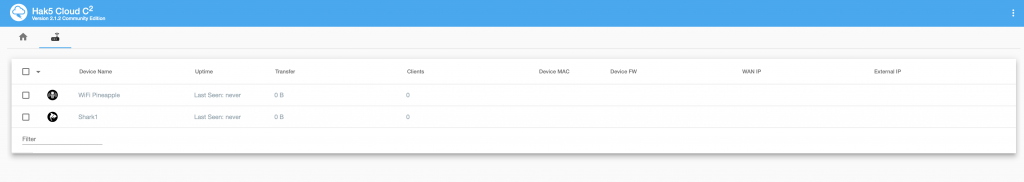
To the Cloud!
Like most of the Hak5 tools, you can remotely manage them via the Cloud C² server. There are the prerequisites of the devices to be configured with an IP, have access to the internet, and for the necessary connect commands to have been implemented for them to reach back. Also, you can use their free version (up to 10 devices managed). The basic steps involve creating a profile in your Cloud C² server, downloading a config script, and then uploading it into the Hak5 device you will be deploying. Further information on the server and configurations can be found here.
How to Mitigate (Updated)
One comment by a friend after reading this article was, “Yo that’s actually scary. These tools are easily accessible and the average person doesn’t know anything about protecting their network.” And he is correct, the average business owner doesn’t know how to protect against a tool like this. We could go back and forth of whether a tool like this fits within the threat profile for a small to medium size business vs. an attack on their external websites/payment systems. That being said, there are a few ways that the potential of this type of tool can be minimized.
The Wrap Up
This was the first Hak5 network attack toolset that I have written about. I was pleasantly surprised with how easy it was to deploy and successfully test right out of the box. The rest of the management and access was very straight forward. I could see this being a very useful tool in pentest and red team engagements to gather basic information.
I have a few more Hak5 tools that I will be testing out next (Wifi Pineapple, Packet Squirrel, Owl, Bash Bunny, Rubber Ducky, Lan Turtle, Plunder Bug, and Screen Crab). Lastly, as I mentioned above, this information is for educational purposes only. You should only use tools/techniques like this on equipment/networks that you are authorized to do so. Don’t do something illegal and don’t be an ass! Baby Yoda would be highly disappointed!
Shark jack что это
1. Buy Variable Woman’s House.
2. Clean outside of house first. Make sure every window is clean and the house is completely cleaned inside and out and all radiators are mounted! Kill all Cockroaches!
3. First room on right sell shelves and clean windows
4. Sell everything in the Kitchen, even the counters. there should be nothing in there at all
5. Sell everything in living room exept coffee table and leave coffee table were it is
6. 1st Bedroom on left sell everything
7. Bathroom on right sell sink and toilet and heating radiator, roaches are hiding behind radiator.
Then buy sink 47.40 and toilet 53.29 and replace radiator
8. In Master bedroom sell the 2 shelves, then in closet sell the shelves
9. Master bathroom sell shower and sink and buy new shower and moutable sink 47.40
10. In master bedroom buy single bed Mantis 100.70 and that’s all for master bedroom
11. There are 2 more bed rooms. make sure that you sell all furniture in both bedrooms, then the bedroom at the end of the hall the gray one buy Single bed Mantis 100.70 and that is all, so in master bedroom and the gray bedroom at the end of the hall all you should have is 1 single bed Mantis 100.70
12. In living Room buy Couch Archaic 139.97 and put under window in front of coffee table that you left there. then for TV buy Monitor 109.39 and place on coffee table facing couch. Now this is important, buy Refrigerator Mono 196.07 then place to left of couch in corner in living room.
Want that achievement faster? No problem, check out the new Version from «cletgdm»:
Thanks for giving me the right to publish that nice idea 😀
Paul & Shark оригинал vs подделка
Мы тут постарались собрать для вас основные моменты, на которые стоит обращать внимание, если хочешь приобрести оригинальную продукцию культового итальянского бренда «Paul & Shark».
— во-первых, начнём с того, что все изделия бренда производятся только в Италии. Никакого Китая, Турции или других стран в качестве изготовителя значится не должно. Кстати, именно Турция, а не Китай, является основным поставщиком поддельных изделий «Paul & Shark».
— во-вторых, везде придерживайтесь золотого правила – прежде чем покупать, неплохо посетить сайт компании. Там можно посмотреть официальную информацию о магазинах, предлагающих продукцию бренда, познакомиться с новыми коллекциями, узнать свежие новости. А также на официальном сайте вы можете вступить в клуб «Paul & Shark», членство в котором даст вам некоторые привилегии (скидки, подарки, начисление бонусов и т.п.).
— покупая вещь в интернет-магазине, обратите внимание, на сколько подробно описаны её детали и особенности, а также сколько фотографий для рассмотрения представлено. Правильным будет выбрать того продавца, который предоставляет максимум информации и несколько разноплановых снимков.
— изделия «Paul & Shark» относятся к высшая ценовая категория, поэтому предложения тип «одежда «Paul & Shark» недорого» должны вызывать сомнения. Вещи итальянского бренда стоят столько, сколько стоят. То есть их довольно высокая стоимость оправдана – европейской производство, использование высококачественных материалов и современных технологий. Как говорится — если что-то слишком хорошо, чтобы быть правдой, то лучше перепроверить.
— кстати, о материалах. Учитывайте их особенности, при выборе изделия. Особенно это касается технологичных тканей. У бренда немало собственных уникальных «фишек» в дизайне, крое, маркетинге и, в том числе, он может похвастаться собственными разработками и использованием инновационных технологий. Это водонепроницаемая, непродаваемая и «дышащая» отделка «Typhoon 20000», технология «E.M.W. Shield», защищающая от электромагнитного излучения, способная преломлять свет водонепроницаемая ткань «LUX JACKET» и т.д. Согласитесь, даже самая качественная реплика не сможет отвечать всем этим характеристикам. Использовать такие технологии и материалы для фейковой продукции кране сложно. Какая ткань или технология использовалась при создании той или иной вещи можно увидеть на самом изделии – эта информация обозначается на ярлыке.
Если вещь, которую вы планируете приобрести, изготовлена не из технологичной ткани и без использования инновационных технологий, например, это хлопковое поло, то и здесь есть чем себя обезопасить от покупки контрафактной продукции.
— каждое изделие «Paul & Shark» имеет идентификационный код на прикрепленных к ним картонных бирках, либо на внутренней бирки изделия с QR-кодом который содержит информацию о номере модели, её цвете, размере. Также каждая вещь обозначается номером партии, в которую она вошла. Все эти данные можно проверить, отправив их через официальный сайт бренда, либо через сайт www.certilogo.com где вам довольно оперативно ответят — оригинальную ли продукцию вы держите в руках.
— трикотажные вещи бренда имеют небольшую белую или синюю петельку, спрятанную под квадратным ярлычком, пришитом к внутренней стороне горловины.
— все картонные этикетки прикреплены к изделию на витом шнурке синего цвета.
Проведите тщательный стандартный анализ вещи, ещё раз пощупайте ткань, на сколько аккуратно выполнены все детали.
— осмотрите логотип, патч – ровные ли буквы, на сколько красиво, пропорционально они сделаны. Обратите внимание на шрифт – у «Paul & Shark» он неизменен, всегда один и тот же.
— заострите внимание на фурнитуре, на сколько она качественная, прочная. У оригинала будут брендированные пуговицы, кнопки и даже на зажимах утяжек у капюшона, например, вы увидите выгравированную акулу.
Еще такой момент – прежде чем приступать к покупке, лучше познакомиться с особенностями той вещи, которая вам понравилась. Дело в том, что, во-первых, у бренда свой характерный фирменный стиль и часто в дизайне используются такие декоративные детали, как цветная окантовка, фигурный или контрастный шов, оригинальное сочетание цветов, дизайнерские принты и т.д. И во-вторых, у каждой линейки одежды («Typhoon», «Bretagne», «Yachting»), выпускаемые брендом, свои особенности.
— компания использует качественную и красивую упаковку, никаких так называемых «пылевых» мешков или дешёвых пакетов. Более дорогостоящие изделия «Paul & Shark» упаковывает в фирменные металлические контейнеры или в большие сумки.
Компания «Paul & Shark» существует на международном рынке более 40 лет и всё это время придерживается принципам честного и качественного производства, уделяя максимум внимания самым мелким деталям при создании стильных, красивых комфортных и технологичных вещей. Это один из тех брендов, вещи которого, вне зависимости от стоимости, хочется иметь только оригинальные.
Если у вас есть дополнения, пишите в комментариях, будем рады вашей помощи! а приобрести оригинальный Paul Shark вы можете здесь